ISG re350 poppy
ISG re350 poppy
* 题目
这是一道mac的题,这是一道歧视穷人的题。
这是一道用到curl库的题,后面写打印flag的程序的时候也要用到curl,琢磨了一段时间才搞起。最大的收获就是学会了这种第三方lib库的使用吧。
* 思路
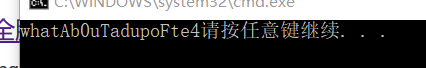
如图 把输入带进sub_100000FD0函数和sub_100000CF0函数加密过后与aN比较,相等的话就输出”The flag is: \n”,和题目提示没有输出的输出相对应。因为看aN的内容他肯定不是flag。
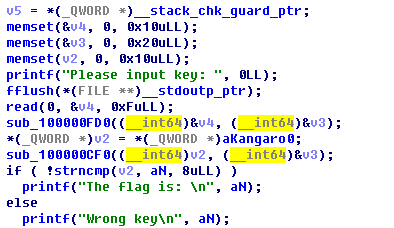
而且sub_100000CF0这个函数让人很头疼,我是看不懂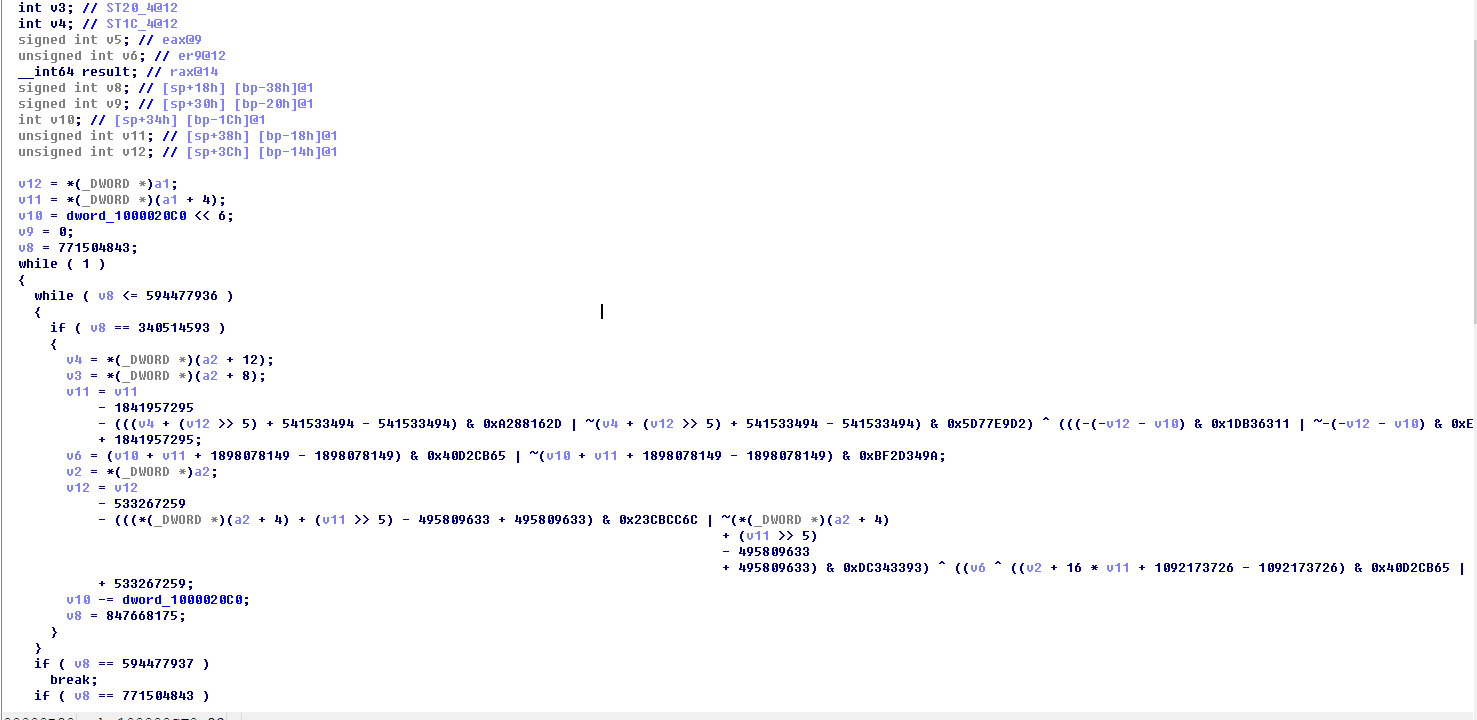
这是aN的内容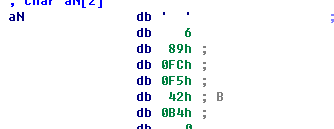
其实aN这么少完全可以爆破得到正确输入,不过得到了貌似也没用,并不会输出真正的flag。
* 解决办法
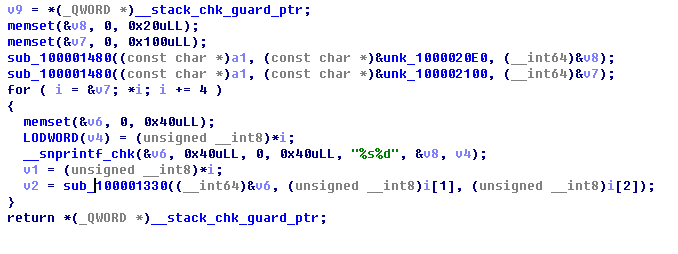
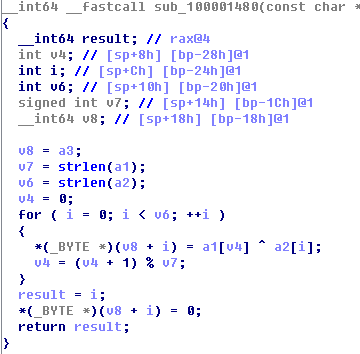
从sub_100001530入手,它里面所调用的一个sub_100001210函数是可以看到调用了curl库并且去网上爬了什么东西。那么sub_100001480加密得到的v8开头必定是https:或者http:/。
由此可以反推出正确的v3字符串,是T0mato。得到一个网址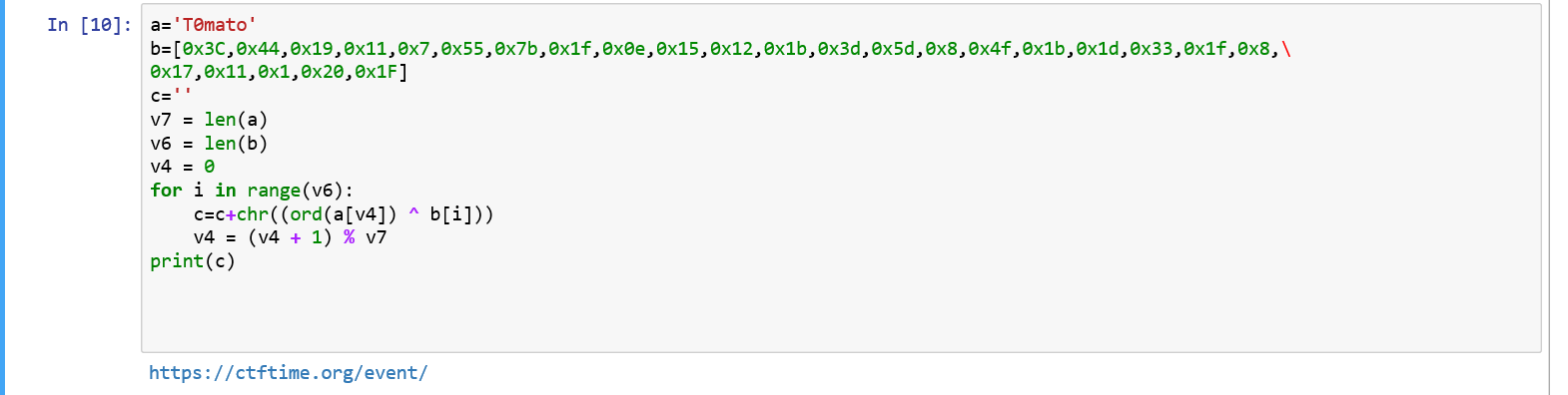 和一个数组
和一个数组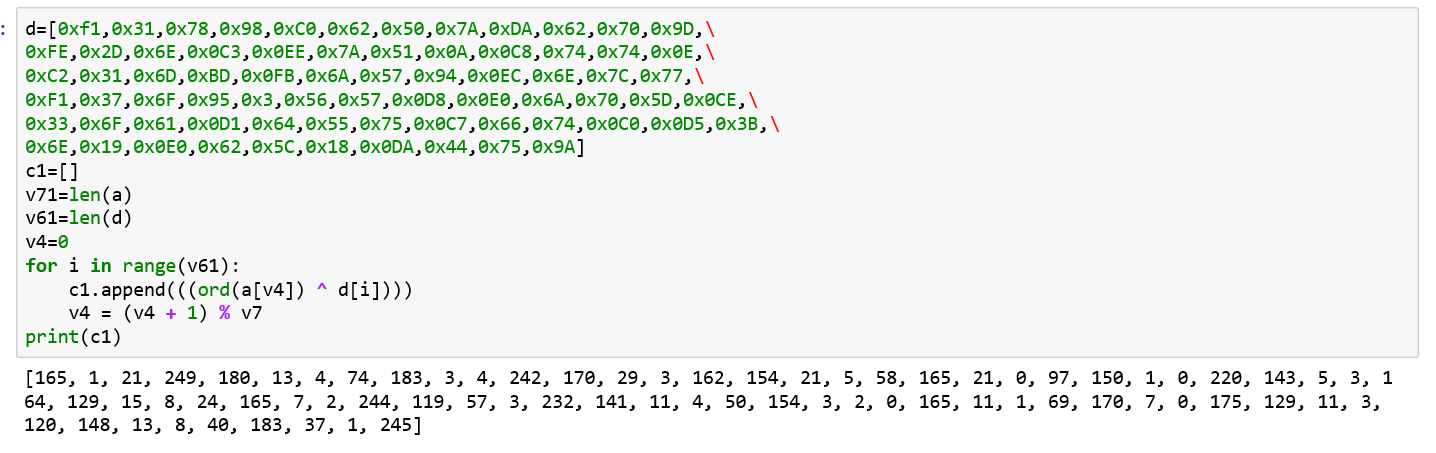 。
。
* 答案
关键是知道了该输入什么也没法运行拿到的程序,如果可以的话直接调试一下在sub_100001330处断点看下每次爬的是什么就知道答案了。
然而穷逼有穷逼的方法,穷逼自己编译一个程序看看爬下来的是什么。以下是代码1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
39
40
41
42
43
44
45
46
47
48
49
50
51
52
53
54
55
56
57
58
59
60
61
62
63
64
65
66
67
68
69
70
71
72
73
74
75
76
77
78
79
80
81
82
83
84
85
86
87
88
89
90
91
92
93
94
95
96
97
98
99
100
101
102
103
104
105
106
107
108
109
110
111
112
113
114
115
116
117
118
119
120
121
122
123
124
125
126
127
128
129
130
131
132
133
134
135
136
137
138
139
140
141
142
143
144
145
146
147
148
149
150
151
152
153
154
155
156
157
158
159
160
161
162
163
164
165
166
167
168
169
170
171
172
173
174
175
176
177
178
179
180
181
182
183
184
185
186
187
188
189
190
191
192
193
194
195
196
197
198
199
200
201
202
203
204
205
206
207
208
209
210
211
212
213
214
215
216
217
218
219
220
221
222
223
224
225
226
227
228
229
230
231
232
233
234
235
236
237
238
239
240
241
242
243
244
245
246
247
248
249
250
251
252
253
254
255// poppy.cpp : 定义控制台应用程序的入口点。
//
__int64 __fastcall sub_100001740(const char *a1, int a2, char *a3, int a4, int a5)
{
signed int v5; // eax@42
signed int v6; // eax@45
signed int v7; // eax@48
signed int v8; // eax@53
signed int v9; // eax@57
signed int v10; // eax@62
signed int v11; // eax@65
bool v13; // [sp+7Bh] [bp-45h]@0
signed int v14; // [sp+7Ch] [bp-44h]@1
char *v15; // [sp+80h] [bp-40h]@0
char *v16; // [sp+88h] [bp-38h]@0
int v17; // [sp+94h] [bp-2Ch]@0
int v18; // [sp+98h] [bp-28h]@1
int v19; // [sp+9Ch] [bp-24h]@1
char *v20; // [sp+A0h] [bp-20h]@1
signed int v21; // [sp+B8h] [bp-8h]@0
int v22; // [sp+BCh] [bp-4h]@1
v20 = a3;
v19 = a4;
v18 = a5;
v22 = a5;
v14 = 687849597;
do
{
while (v14 > -721349906)
{
if (v14 > -251959739)
{
if (v14 > 1643955)
{
if (v14 > 2139374635)
{
if (v14 == 2139374636)
{
v11 = 1996424361;
if (v17 < v18)
v11 = -251959738;
v14 = v11;
}
}
else if (v14 > 111058115)
{
if (v14 > 319798562)
{
if (v14 > 497514003)
{
if (v14 > 687849596)
{
if (v14 > 1056727273)
{
if (v14 > 1629186829)
{
if (v14 > 1841852057)
{
if (v14 > 1996424360)
{
if (v14 == 1996424361)
{
v21 = (DWORD)v15 - (DWORD)v20;
v14 = -2127602345;
}
}
else
{
switch (v14)
{
case 1841852058:
v6 = 111058116;
if (a2 <= 0)
v6 = 319798563;
v14 = v6;
break;
case 1892047314:
v8 = -721349905;
if (v17 < v18)
v8 = 497514004;
v14 = v8;
v13 = 0;
break;
case 1914277125:
v10 = 2139374636;
if (!v15)
v10 = -251959738;
v14 = v10;
break;
}
}
}
else if (v14 == 1629186830)
{
v16 += (signed int)v15 - (signed int)v16 + 1;
v14 = 1643956;
}
}
else if (v14 == 1056727274)
{
v17 = 0;
v16 = v20;
v14 = 1892047314;
}
}
else if (v14 == 687849597)
{
v5 = 1841852058;
if (v22 <= 0)
v5 = 319798563;
v14 = v5;
}
}
else if (v14 == 497514004)
{
v15 = strstr(v16, a1);
v14 = -721349905;
v13 = v15 != 0LL;
}
}
else if (v14 == 319798563)
{
v21 = -1;
v14 = -2127602345;
}
}
else if (v14 == 111058116)
{
v7 = 1056727274;
if (v19 <= 0)
v7 = 319798563;
v14 = v7;
}
}
else if (v14 == 1643956)
{
++v17;
v14 = 1892047314;
}
}
else if (v14 == -251959738)
{
v21 = -1;
v14 = -2127602345;
}
}
else if (v14 == -721349905)
{
v9 = 1914277125;
if (v13)
v9 = 1629186830;
v14 = v9;
}
}
} while (v14 != -2127602345);
return (unsigned int)v21;
}
size_t sub_1000011C0(void* a1, size_t a2, size_t a3, void* a4)
{
__int64 v4; // ST18_8@1
v4 = a3;
//memset(data, 0LL, 0x1000000LL);
int size = strlen((char*)a4);
int len = size_t(a3*a2);
if (size == 0)
strcpy_s((char*)a4, len + 1, (char*)a1);
else
strcat_s((char*)a4, 0x1000000uLL, (char*)a1);
return size_t(a3*a2);
}
__int64 __fastcall sub_100001210(char* a1, char* a2)
{
CURL *curl; // ST38_8@1
CURLcode res;
memset(a2, 0LL, 0x10000LL);
curl_global_init(3LL);
curl = curl_easy_init();
curl_easy_setopt(curl, CURLOPT_URL, a1);
curl_easy_setopt(curl, CURLOPT_TIMEOUT, 30LL);
curl_easy_setopt(curl, CURLOPT_WRITEFUNCTION, sub_1000011C0);
curl_easy_setopt(curl, CURLOPT_WRITEDATA,a2);
curl_easy_setopt(curl, CURLOPT_SSL_VERIFYHOST, 0LL);
curl_easy_setopt(curl, CURLOPT_SSL_VERIFYPEER, 0LL);
res = curl_easy_perform(curl);
curl_easy_cleanup(curl);
curl_global_cleanup();
return 0LL;
}
__int64 __fastcall sub_100001330(char* a1, unsigned int a2, int a3)
{
int v3; // ST70_4@1
char* v4; // ST60_8@1
int v5; // eax@1
int v6; // eax@1
int v7; // ST5C_4@1
const char *v8; // ST10_8@1
int v9; // eax@1
char v10; // ST4B_1@1
v3 = a3;
v4 = (char *)malloc(0x1000000uLL);
memset(v4, 0LL, 0x1000000LL);
//v4 = data;
sub_100001210(a1, v4);
v5 = strlen(v4);
v6 = sub_100001740("<td>", 4, v4, v5, a2);
v7 = v6;
v8 = &v4[v6 + 4];
v9 = strlen(v8);
v10 = v4[(signed int)(v3 + (unsigned __int64)sub_100001740("\">", 2, (char *)v8, v9, 1) + v7 + 4 + 2)];
free(v4);
return (unsigned int)v10;
}
int main()
{
char url[] = "https://ctftime.org/event/";
int array[] = { 165, 1, 21, 249, 180, 13, 4, 74, 183, 3, 4, 242, 170, 29, 3, 162, 154, 21, 5, 58, 165, 21, 0, 97, 150, 1, 0,220, 143, 5, 3, 164, 129, 15, 8, 24, 165, 7, 2, 244, 119, 57, 3, 232, 141, 11, 4, 50, 154, 3, 2, 0, 165, 11, 1, 69, 170,7, 0, 175, 129, 11, 3, 120, 148, 13, 8, 40, 183, 37, 1, 245,'\0' };
char* v8 = url;
int* v7 = array;
int * i;
char* v6;
__int64 v1;
__int64 v4;
char v2;
for (i = v7; *i; i += 4)
{
v6 = (char*)malloc(0x100);//memset(&v6, 0, 0x40uLL);
WORD(v4) = (unsigned __int8)*i;
_snprintf(v6, 0x40uLL, "%s%d", v8, v4);
v1 = (unsigned __int8)*i;
v2 = sub_100001330(v6, (unsigned __int8)i[1], (unsigned __int8)i[2]);
printf("%c", v2);
}
return 0;
}
最后结果如下